|
|
||
|---|---|---|
| ansible | ||
| doc | ||
| hosts | ||
| kubernetes | ||
| lib | ||
| overlay | ||
| proxmox | ||
| secrets@0efb7df81d | ||
| .gitignore | ||
| .gitmodules | ||
| README.md | ||
| deploy-flake.sh | ||
| flake.lock | ||
| flake.nix | ||
| host-registry.nix | ||
| hq.nixops | ||
| install-host.sh | ||
| nix-maintenance.sh | ||
README.md
Setup
Install Nix Flakes
A Nix environment with Nix Flakes support is required.
(temporary) Shell with Nix Flakes
Set up an environment (with the common command nix-shell) in which the package nixFlakes (for Nix Flakes) is available and jump into it
nix-shell --packages nixFlakes
Nix Flakes ist gegenwärtig bei Nix (Version 20.09) noch keine standardmäßige Funktionalität für Nix. Die Bereitstellung der Kommandos für Nix Flakes müssen als experimentelle Funktionalität für das Kommando ''nix'' festgelegt werden, um sie verfügbar zu machen.
Set some configuration (do this only once)
echo 'experimental-features = nix-command flakes' >> ~/.config/nix/nix.conf
Add this repository to your local flake registry:
nix registry add c3d2 git+https://gitea.c3d2.de/C3D2/nix-config
(permanent) System with Nix Flakes
set this to your NixOS configuration:
{ pkgs, ... }: {
nix = {
package = pkgs.nixFlakes;
extraOptions = "experimental-features = nix-command flakes";
};
}
And add this repository to your local flake registry:
nix registry add c3d2 git+https://gitea.c3d2.de/C3D2/nix-config
Deployment
Beide failen bei Activation des neuen Profils. (TODO)
Mit Flakes
Local deployment
Running nixos-rebuild --flake c3d2 switch on a machine should be sufficient
to update that machine to the current configuration and Nixpkgs revision.
Remote deployment
Use nix run with one of the deploy scripts exported by the flake,
for example: nix run c3d2#glotzbert-nixos-rebuild switch. Use nix flake show c3d2
to show what is available. Note that the deploy scripts only work if
the target machines already has flakes enabled.
Now that there is a -local variant that builds the system profile on
your machine (possibly reusing dependencies that were built for other
hosts), flakification of an existing NixOS host can be done using nix run c3d2#glotzbert-nixos-rebuild-local switch
The must be an existing nixosConfiguration.${host} in flake.nix.
Remote deployment from non-NixOS
A shell script that copies the current working tree, and runs
nixos-rebuild switch on the target:
./deploy-flake.sh hydra.hq.c3d2.de
It cannot not lookup hostnames in host-registry.nix.
It will not take extra care of the secrets.
Mit NixOps
The official way for deployment is through deployer.serv.zentralwerk.org
Deploy changes
Use deployer system:
ssh k-ot@172.20.73.9
cd nix-config/
nixops deploy -d hq --check --include=[hostname]
Creating new Container
This does not work yet, as the nixos-system-x86_64-linux.tar.xz image is broken.
- log into any proxmox server
- pct create [num] cephfs-iso:vztmpl/nixos-system-x86_64-linux.tar.xz -ostype unmanaged -net0 name=eth0,bridge=vmbr0,tag=[vlantag] -storage vms -hostname [hostname]
- adjustments through ui if necessary
- Adjust hq.nixops, add [hostname]
- Run
ssh k-ot@172.20.73.16 cd nix-config/ nixops deploy -d hq --check --include=[hostname]
Tarballs can be built for containers using config.system.build.tarball.
nix build c3d2#nixosConfigurations.dhcp.config.system.build.tarball
Mit nixos-switch rebuild
nixos-rebuild switch -I nixos-config=./hosts/containers/$HOST/configuration.nix --target-host "root@$HOST.hq.c3d2.de"
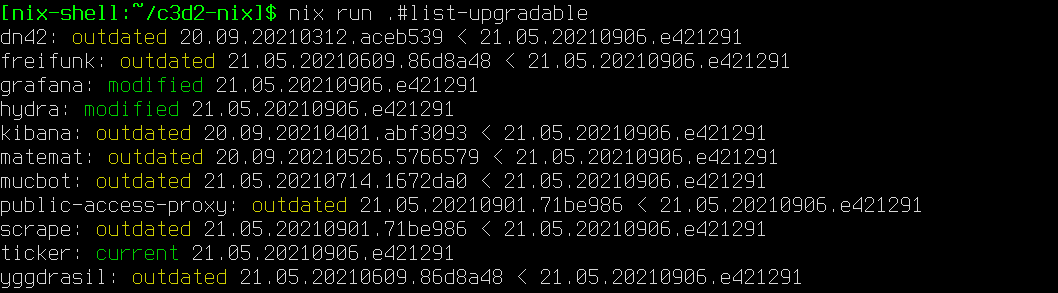
Checking for updates
nix run .#list-upgradable
Checks all hosts with a nixosConfiguration in flake.nix.
Secrets
Add your gpg-id to the .gpg-id file in secrets and let somebody reencrypt it for you. Maybe this works for you, maybe not. I did it somehow:
PASSWORD_STORE_DIR=`pwd` tr '\n' ' ' < .gpg-id | xargs -I{} pass init {}
Your gpg key has to have the Authenticate flag set. If not update it and push it to a keyserver and wait. This is necessary, so you can login to any machine with your gpg key.
Laptops / Desktops
This repository contains a NixOS module that can be used with personal machines
as well. This module appends /etc/ssh/ssh_known_hosts with the host keys of
registered HQ hosts, and optionally appends /etc/hosts with static IPv6
addresses local to HQ. Simply import the lib directory to use the module. As
an example:
# /etc/nixos/configuration.nix
{ config, pkgs, lib, ... }:
let
c3d2Config =
builtins.fetchGit { url = "https://gitea.c3d2.de/C3D2/nix-config.git"; };
in {
imports = [
# ...
"${c3d2Config}/lib"
];
c3d2 = {
isInHq = false; # not in HQ, this is the default.
mapHqHosts = true; # Make entries in /etc/hosts for *.hq internal addresses.
enableMotd = true; # Set the login shell message to the <<</>> logo.
};
# ...
}